Home / CUBESUITE® / CUBE Guest

Thanks to CUBE Guest, small, medium and big companies can plan and record the arrival of visitors by making the access recognition procedure automatic.
How does it work?
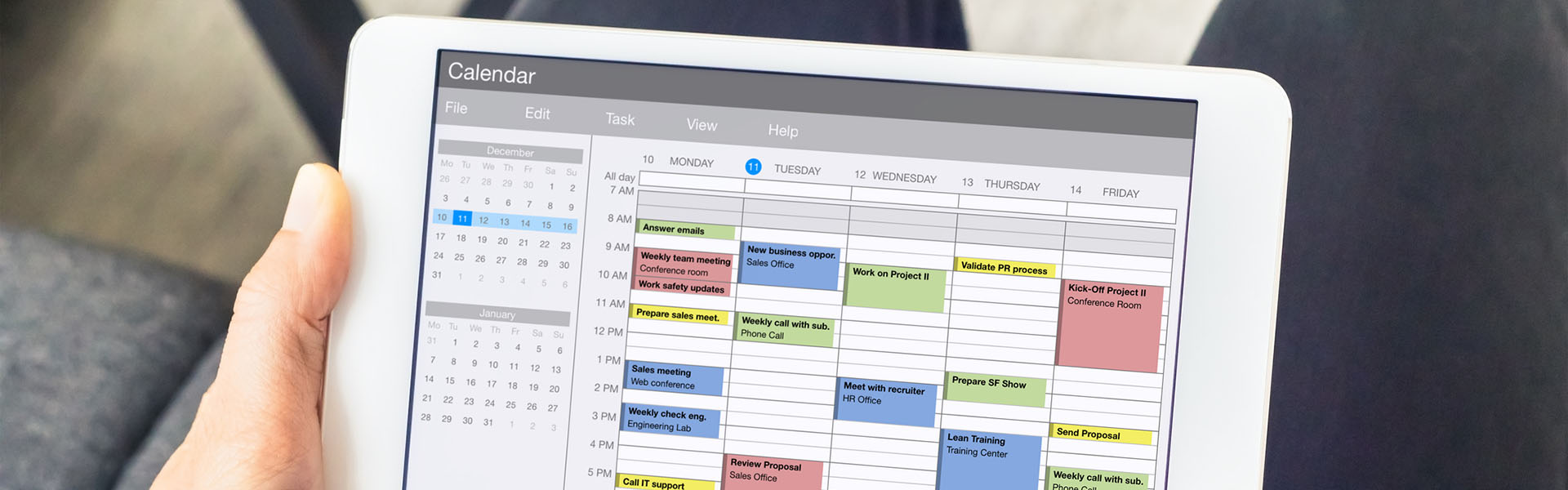
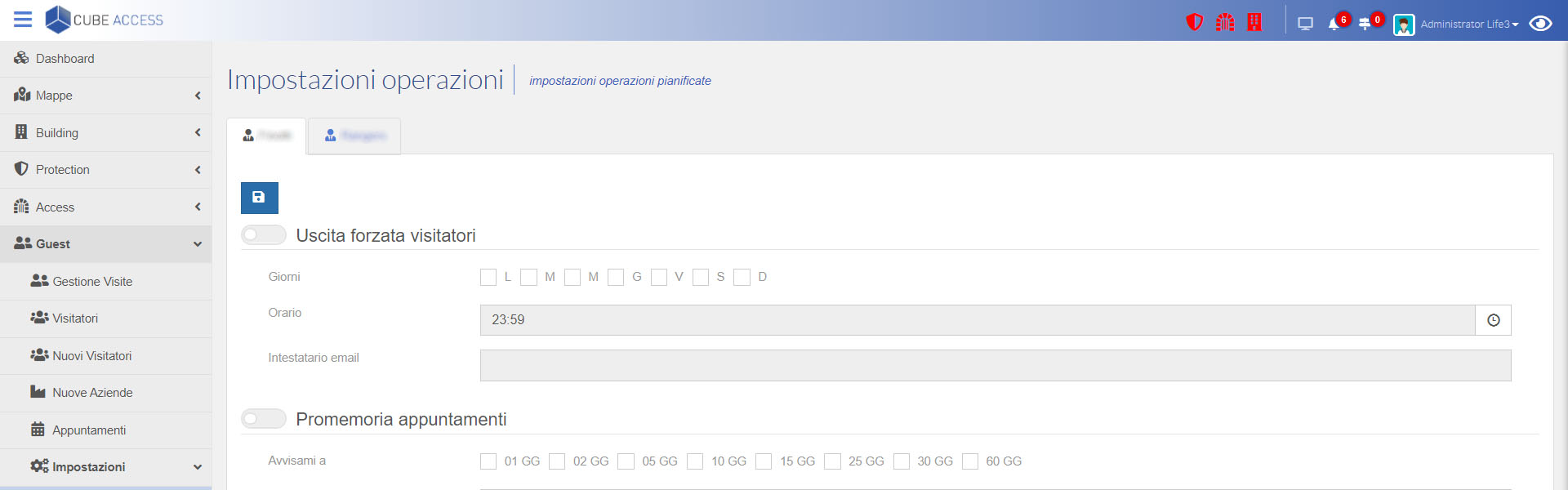
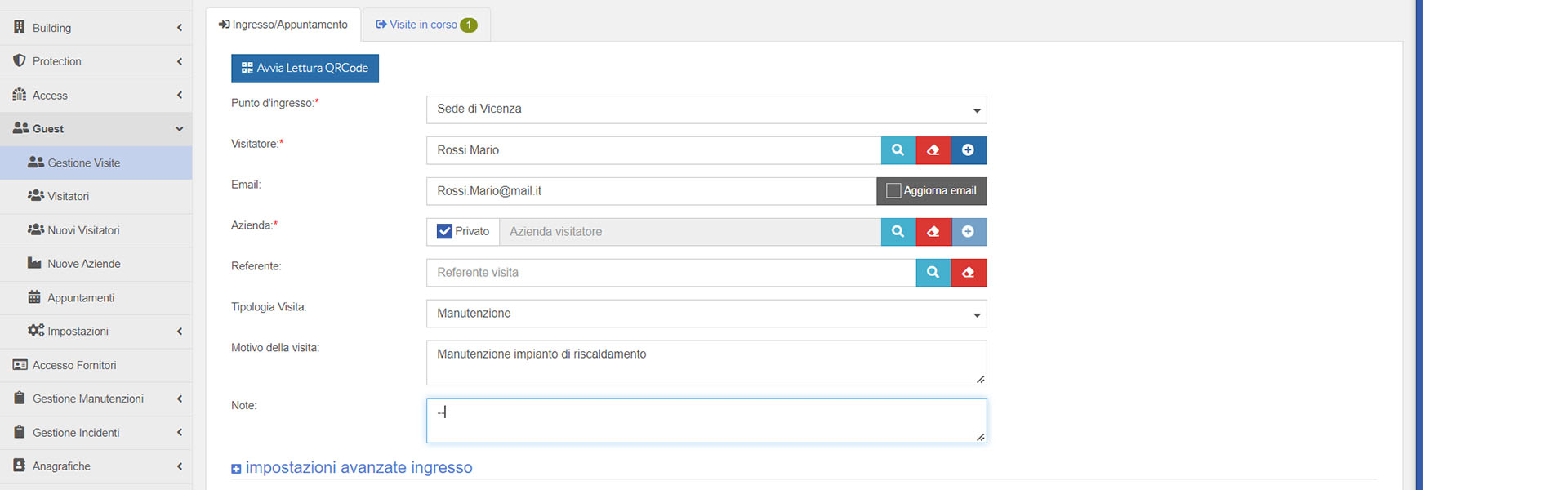
- REGISTRATION: the visitor personal information, the date and time of the appointment and any notes, are registered in the system. An email with the identification QR Code is sent to the visitor
- CHECK IN: through the totem in the hall, the guest can easily check-in by scanning the QR Code
- WAITING ROOM: the contact person receives an email notifying that the guest has arrived and, if it is required, the system prints the safety norms for the guest
- CHECK OUT: at the end of the appointment, the visitor has to scan the QR Code for the second time and CUBE Guest records its exit
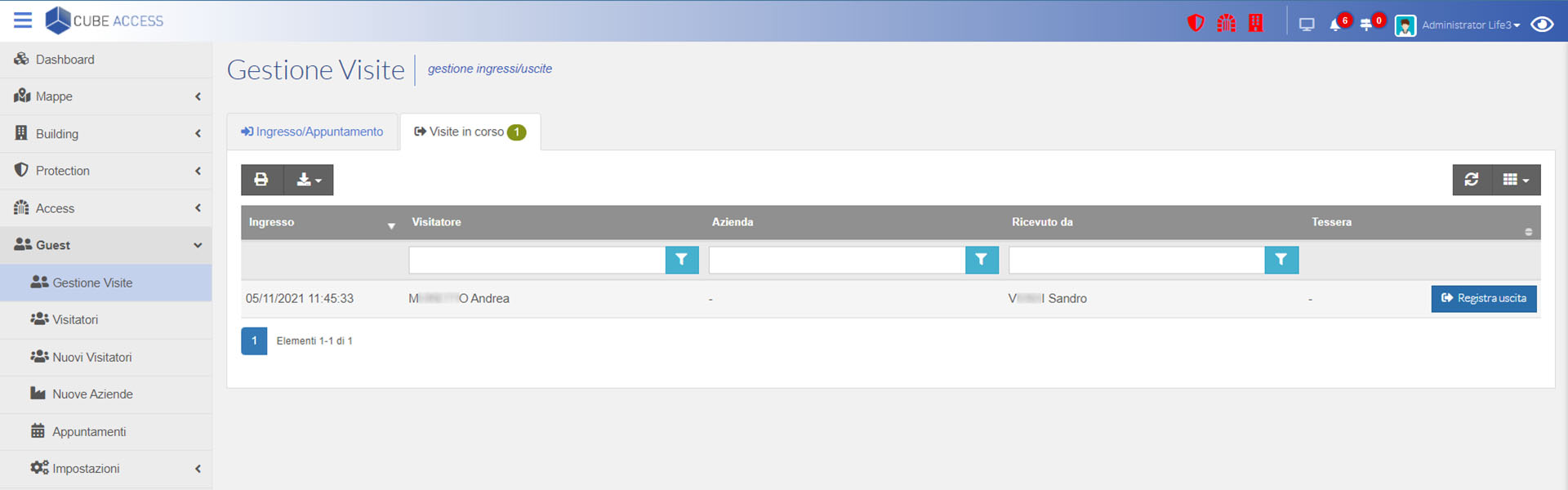
In each moment the user can monitor how many visitors are inside the site and it is possible to make some statistical surveys on the visits duration and how frequent are the visits in each sector and when there is the bigger flow of visitors,…
PRODUCT
FEATURES
Recognizing credentials
Automatic check in
Flows control
Statistics
Black list
Time optimization
CUBE GUEST
CAN BE INTEGRATED AT ANY TIME WITH
ARE YOU INTERESTED IN OUR SOFTWARE?
CUBESUITE® is configured in such a way as to demonstrate compliance with the principles set out in GDPR art.5 and in particular with privacy by default. Where possible, technical measures have been taken to ensure that only the personal data required for each specific purpose of the processing are processed by default.
In particular CUBESUITE® incorporated the following principles:
- Principle of confidentiality: authentication credentials when the user logs in, have an expiration date and an adjustable complexity to ensure the confidentiality of the processed information and to prevent the access by unauthorized users. It is also possible to create unlimited user profiles by assigning them specific privileges, such as deleting and/or exporting data
- Principle of minimization: the Suite is designed in such a way as to allow the erasing of data through the automatic or manual cleaning of the records
- Data security: data can be backed up by integrating them with the customer backup and/or disaster recovery procedures
- Encryption: all software related files are encrypted on file system with an AES 256 encryption key, communications are certified with the customer’s SSL certification, the database is protected by a password and the password is encrypted
- Durability of files uploaded by the user: a file hash is calculated for each uploaded file as to show the inalterability of the data
If you are interested in our product and you want some more information about it, please send us an e-mail at info@life3.it or request a demo by following this link: Request a demo