Home / CUBESUITE® / CUBE Protection®

CUBE Protection® provides an overview about the security and safety systems operating in the building (intrusion detection, fire protection, video surveillance) and it allows to easily manage arming and disarming the alarm systems, verify the area status and schedule automatic operations.
Everything that happens in the system, it will be notified in real-time through pop-up, mail or Telegram.
The software allows the user to:
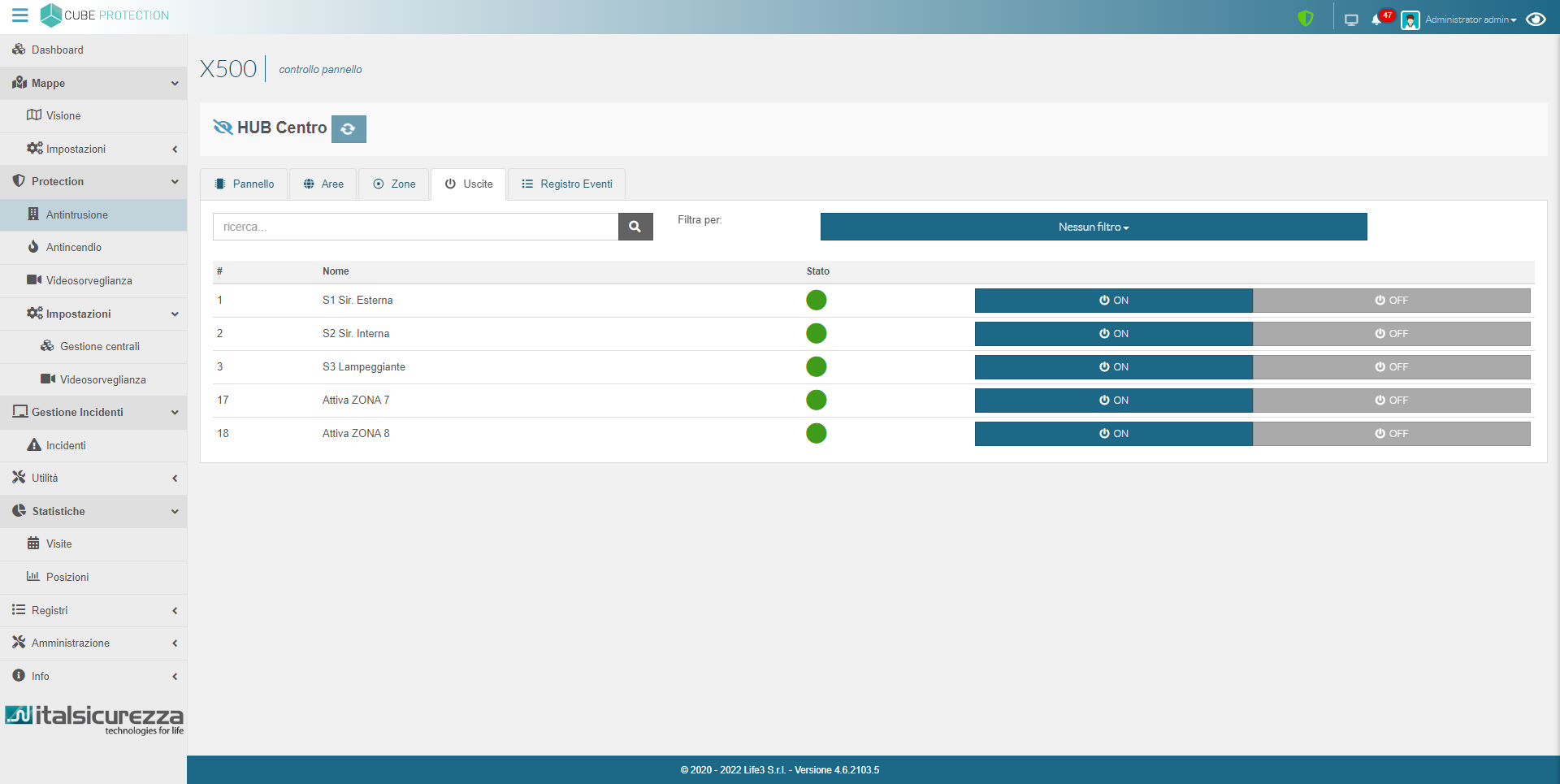
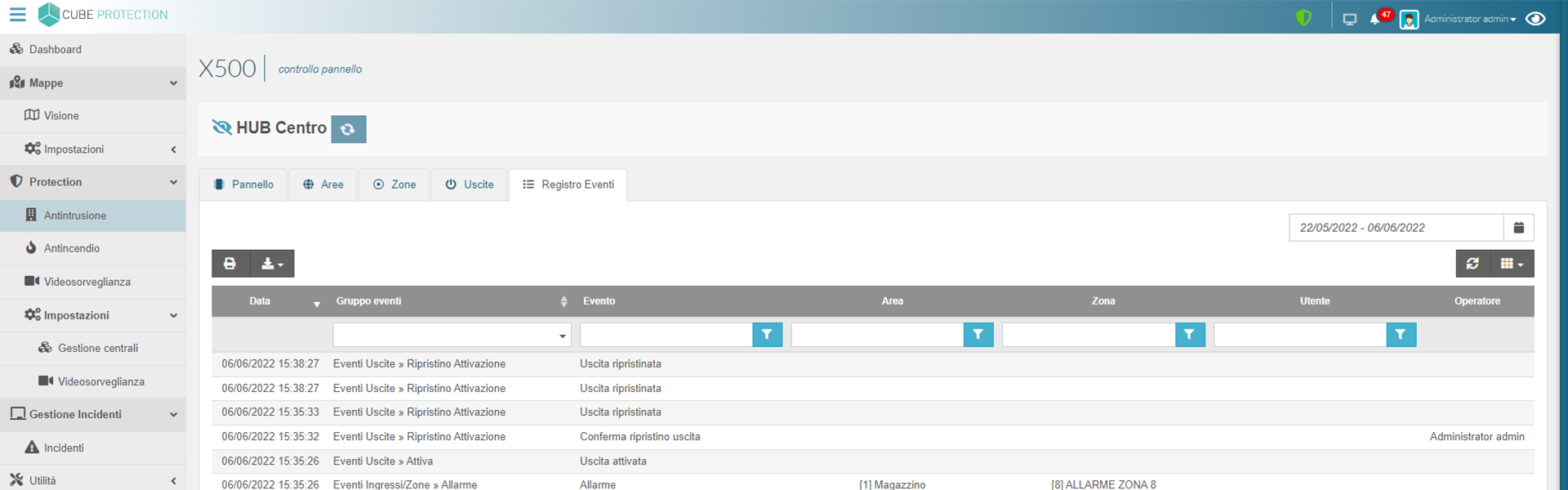
- Visualize the events in real time and access the registers to analyze the events records
- Decide on which system you want to work and open the management page with a simple click
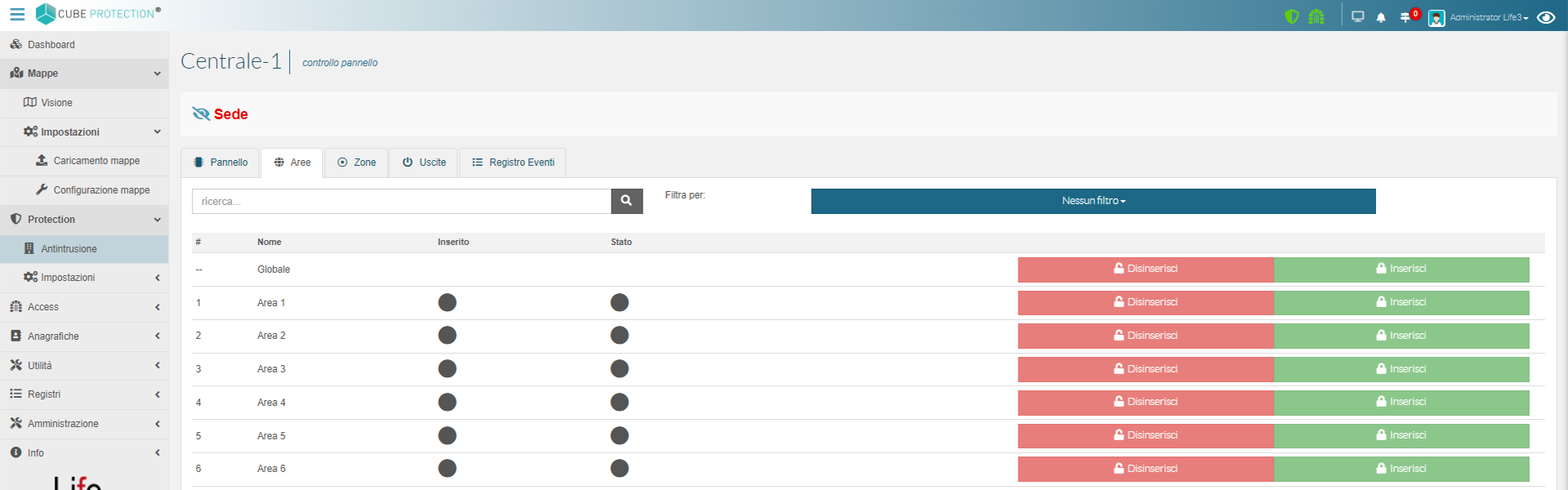
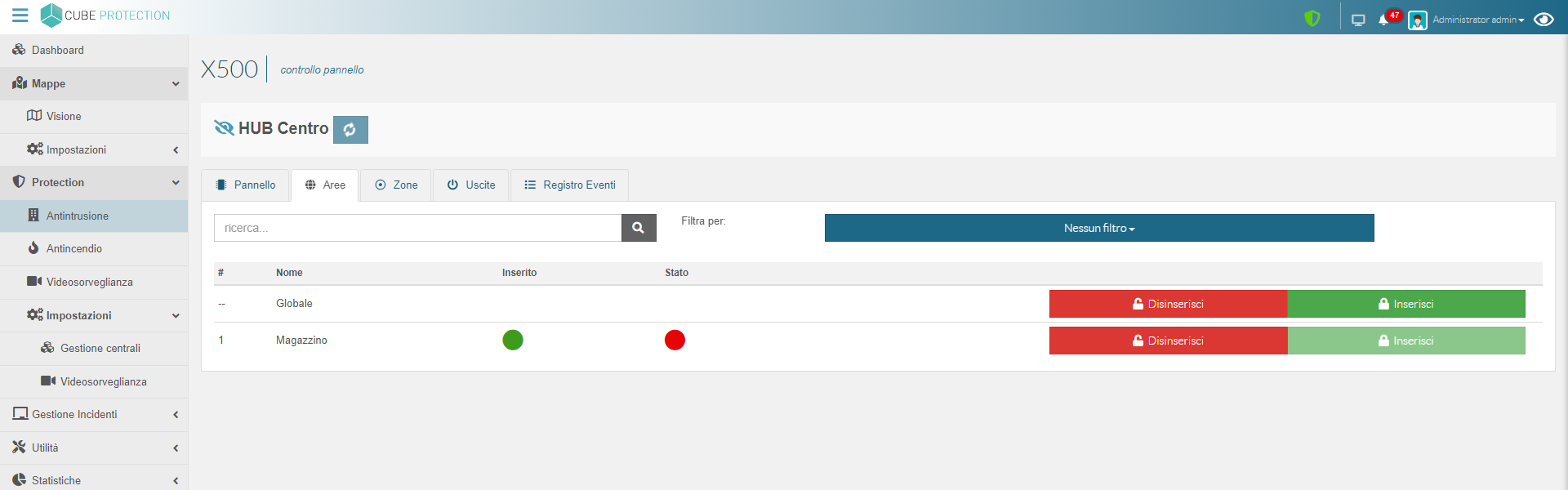
- Switch on and off the intrusion detection system
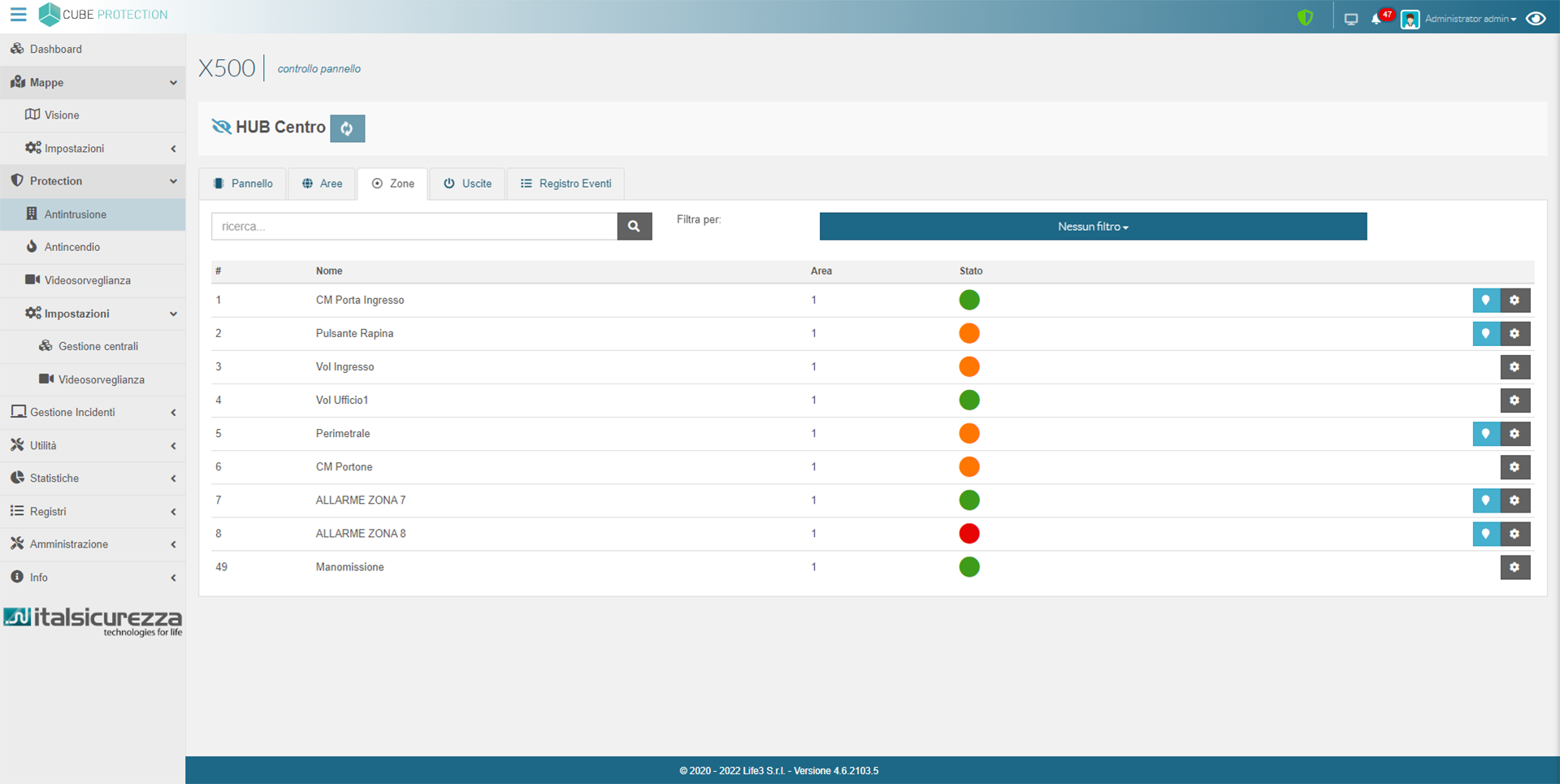
- Visualize the areas status (able – enable – alert – masking – failure…)
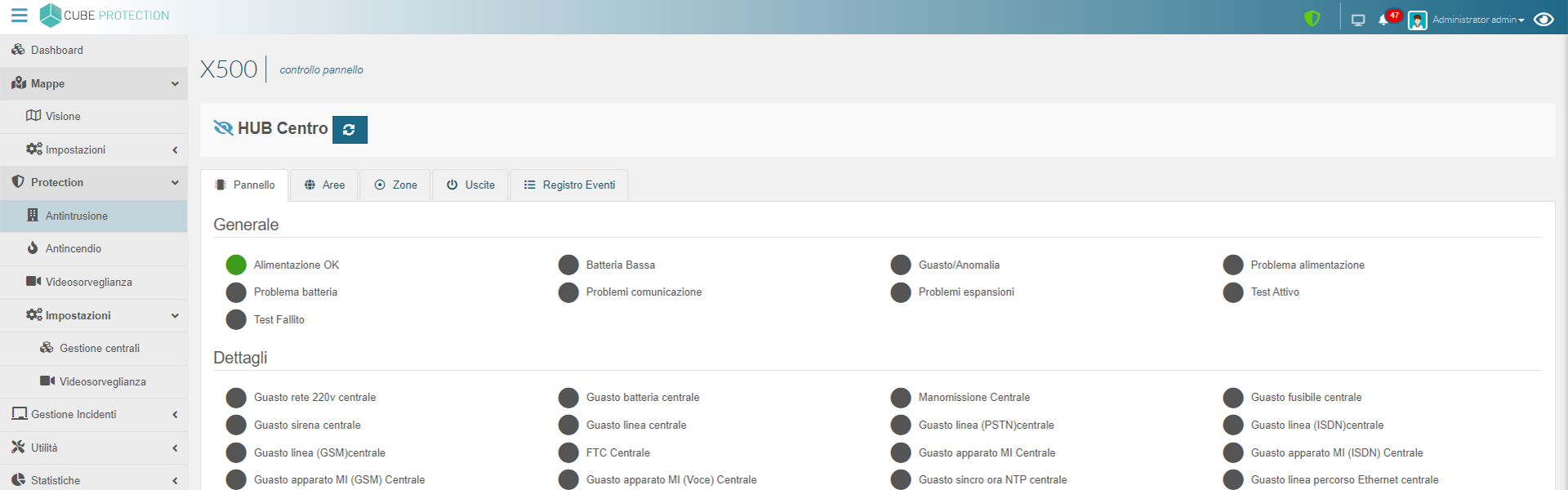
- Visualize the system anomalies and receive alarms or notifications on an event by pop-up, mail or Telegram
- Visualize each detector status on graphic maps too. The color is related to the status in real time and by clicking on the icon you can interact with a single device
- Plan scheduled actions
PRODUCT
FEATURES
Fire monitoring
Theft monitoring
Video surveillance
Controls
Alarm management
Scheduled operations
Reports
Safety health care
CUBE PROTECTION®
CAN BE INTEGRATED AT ANY TIME WITH
ARE YOU INTERESTED IN OUR SOFTWARE?
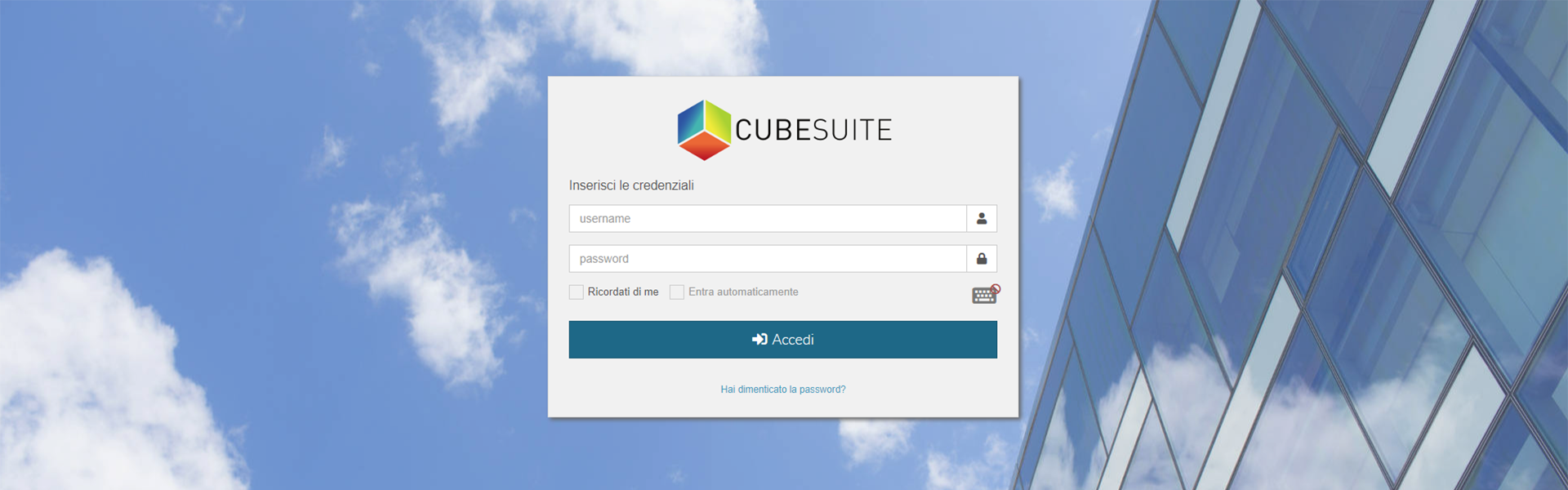
CUBESUITE® is configured in such a way as to demonstrate compliance with the principles set out in GDPR art.5 and in particular with privacy by default. Where possible, technical measures have been taken to ensure that only the personal data required for each specific purpose of the processing are processed by default.
In particular CUBESUITE® incorporated the following principles:
- Principle of confidentiality: authentication credentials when the user logs in, have an expiration date and an adjustable complexity to ensure the confidentiality of the processed information and to prevent the access by unauthorized users. It is also possible to create unlimited user profiles by assigning them specific privileges, such as deleting and/or exporting data
- Principle of minimization: the Suite is designed in such a way as to allow the erasing of data through the automatic or manual cleaning of the records
- Data security: data can be backed up by integrating them with the customer backup and/or disaster recovery procedures
- Encryption: all software related files are encrypted on file system with an AES 256 encryption key, communications are certified with the customer’s SSL certification, the database is protected by a password and the password is encrypted
- Durability of files uploaded by the user: a file hash is calculated for each uploaded file as to show the inalterability of the data
If you are interested in our product and you want some more information about it, please send us an e-mail at info@life3.it or request a demo by following this link: Request a demo